The Era of
Passive Security
Is Over
Penetration testing told you what was broken yesterday. We deploy zero-footprint algorithmic telemetry to map what will break tomorrow.
Preemptive
Cartography.
Threat actors no longer rely on manual probing. They deploy autonomous bots to scan, map, and exploit vulnerabilities at scale. Relying on an annual IT compliance checklist is a foundational liability.
Omnitron operates on a different paradigm. We deploy mathematical modeling, zero-footprint OSINT telemetry, and Post-Quantum cryptographic simulations to fundamentally shift your organization from passive defense into Active Disruption.
> DEFENSE EVOLUTION: AUDIT → MAP → DISRUPT
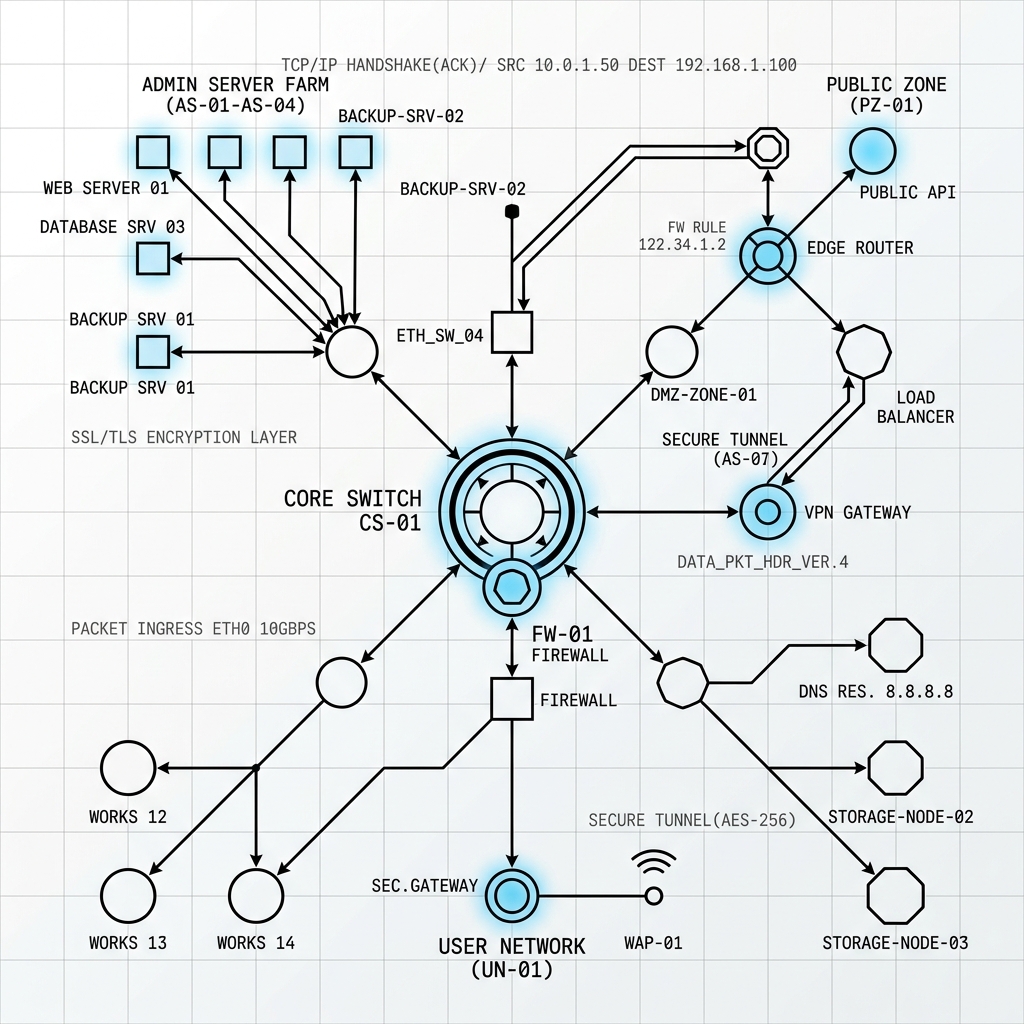 FIG 02. ALGORITHMIC ATTACK SURFACE TOPOLOGY
FIG 02. ALGORITHMIC ATTACK SURFACE TOPOLOGYThe Collapse of Point-In-Time Compliance.
For decades, the standard for corporate security has been the Annual Penetration Test. Organizations pay a vendor to simulate an attack, produce a PDF report of vulnerabilities, and wait for IT teams to patch them over the coming months. This is Point-in-Time Compliance.
In an era of generative AI and autonomous threat actors, this model is mathematically obsolete. As noted by the Gartner Continuous Threat Exposure Management (CTEM) framework, attackers do not operate on an annual schedule. They employ autonomous scripts to continuously reconnoiter external footprints, mapping forgotten cloud instances, unpatched edge routers, and exposed deep-web credentials the second they appear.
By 2026, organizations prioritizing their security investments based on a Continuous Threat Exposure Management (CTEM) program will realize a two-thirds reduction in breaches. Testing must transition from a static, compliance-driven check to an ongoing operational cycle of scoping, discovery, validation, and disruption.
We must move from Testing to Cartography.
Penetration testing assumes the perimeter is static. Attack Surface Cartography assumes the perimeter is constantly degrading. By applying continuous algorithmic telemetry, we chart the threat topography in real-time. We don't just find vulnerabilities; we trace inauthentic botnets back to their C2 infrastructure and calculate the exact timeline of your encrypted records failing to quantum threshold decoding.
If your organization is still waiting for an annual vulnerability report, you are not engaging in cybersecurity. You are engaging in historical record-keeping. The sovereign enterprise demands active, preemptive disruption.
The Sovereign Arsenal
Our intelligence engines map the external threat topography so your internal licensed IT teams know exactly where to build walls.
_
_
_
_
_
_
_
OMNITRON OPERATES STRICTLY AS AN ADVANCED INTELLIGENCE AND THREAT ADVISORY AGENCY. WE DO NOT PROVIDE, SELL, OR EXECUTE PENETRATION TESTING (PTaaS), NOR DO WE DEPLOY LIVE MANAGED SECURITY OPERATIONS CENTRE (SOC) MONITORING AGAINST CLIENT NETWORKS. ALL INTELLIGENCE IS PASSIVELY GATHERED VIA OPEN-SOURCE TELEMETRY, EXTERNAL DATA LAKE CORRELATION, OR THROUGH POST-INCIDENT FORENSIC ISOLATION PROVIDED BY THE CLIENT.